Continuous Verification: Security Onion Alerts → Case Workflow
Zero Trust doesn’t stop at “who logged in.” It assumes compromise and continuously inspects behavior.
In this lab I generated reconnaissance traffic, captured it as a PCAP, ingested it into Security Onion,
validated detections, and escalated an alert into a case—showing how monitoring closes the gap after access is granted.
Overview (My POV)
This wasn’t “look at alerts.” I built a mini detection loop: create hostile behavior (scanning),
capture ground-truth packets, ingest telemetry into a detection platform, then investigate and
escalate. The value is the mindset: access does not equal trust—behavior must be inspected continuously.
What I Actually Did
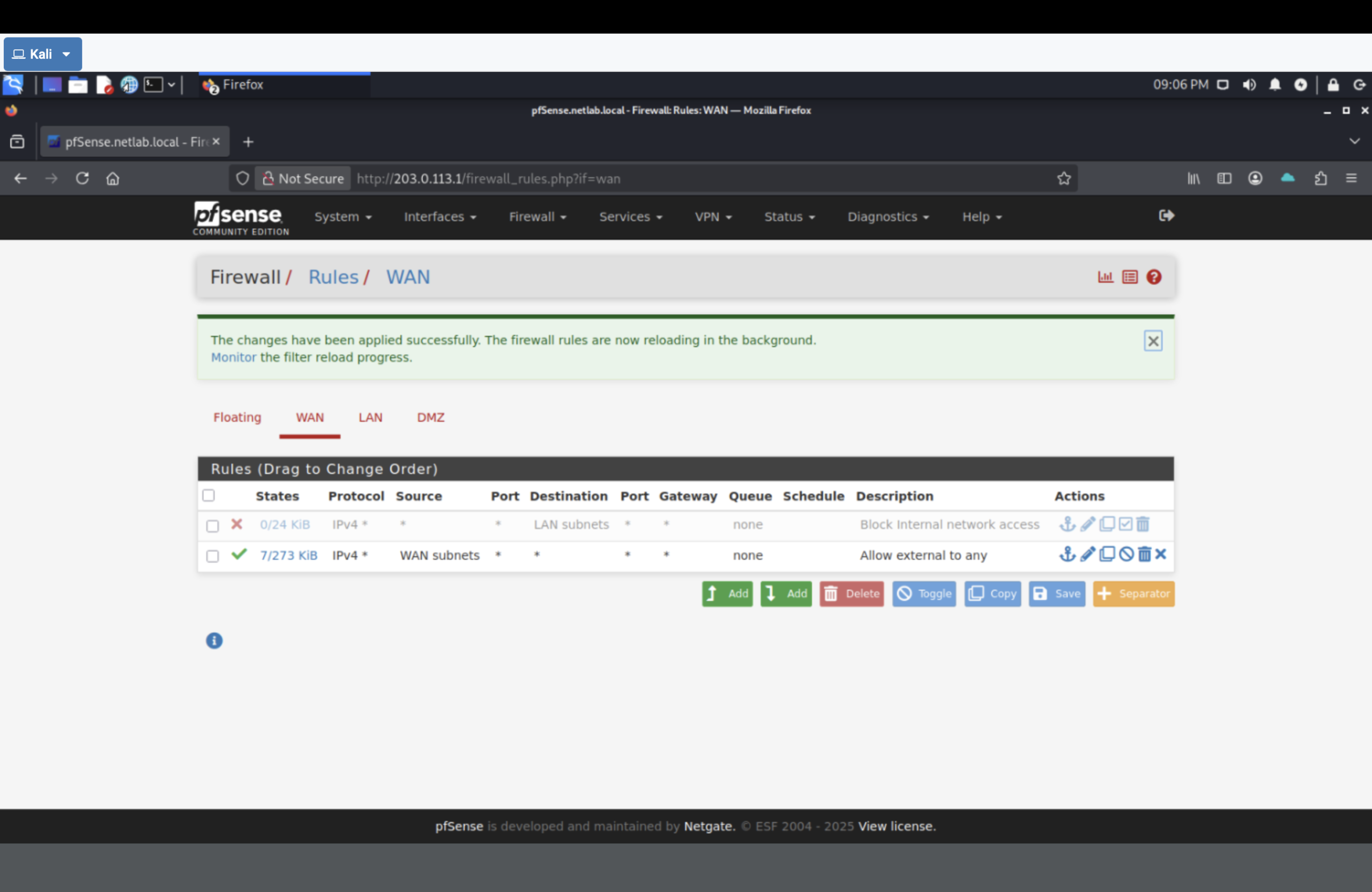
- Temporarily adjusted firewall rules to allow controlled hostile traffic for analysis.
- Captured scanning traffic in Wireshark and saved it as
scan.pcap. - Transferred the PCAP to Security Onion and verified service health.
- Imported the PCAP and reviewed detections on the Alerts dashboard.
- Drilled down on an nmap-related alert and escalated it into a case.
Why This Is Zero Trust
Zero Trust assumes compromise. Even authenticated access can be abused—so we continuously inspect behavior.
- Pre-access controls: identity + firewall boundaries (who can reach what)
- Post-access controls: detections + investigations (what they’re doing once inside)
- Evidence: alerts tied to packet-level proof and a documented case workflow
Detection Loop (what I built)
Hostile behavior (nmap scans)
↓
Packet capture (Wireshark PCAP)
↓
Ingest telemetry (Security Onion import)
↓
Alerts (NIDS/HIDS detections)
↓
Investigation (drilldown + PCAP evidence)
↓
Decision (escalate → case → close)
The point is proving you can move from raw network truth to a defendable investigation outcome.
Key Commands
# Generate recon traffic (Kali) nmap -T5 203.0.113.1 192.168.0.0/24 172.16.1.0/28 nmap -T4 -A -v 172.16.1.10 # Transfer PCAP (Kali) python3 -m http.server # Verify + ingest PCAP (Security Onion) sudo so-status sudo so-import-pcap ~/Downloads/scan.pcap
Proof Gallery (minimal, high-signal)
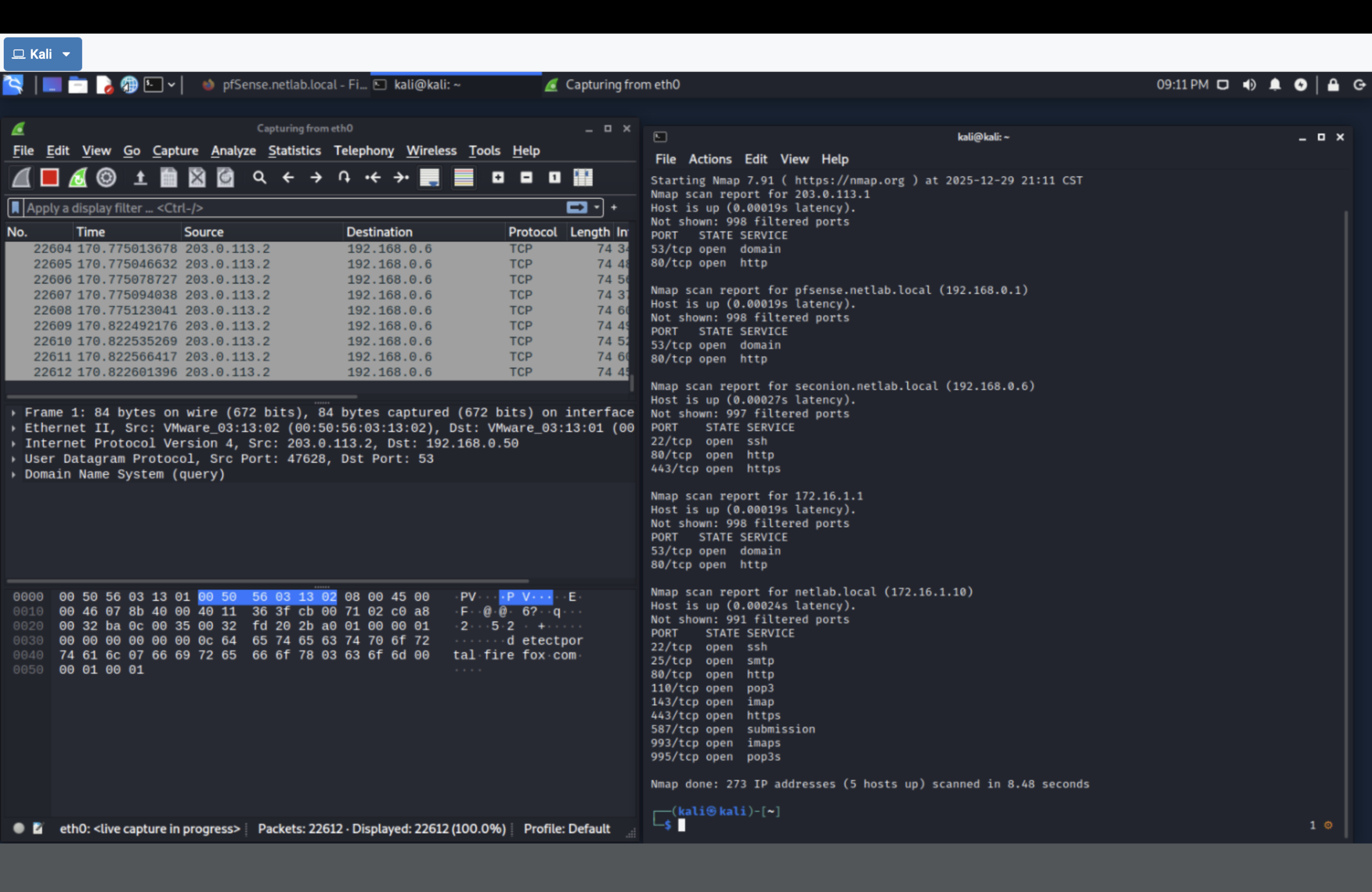
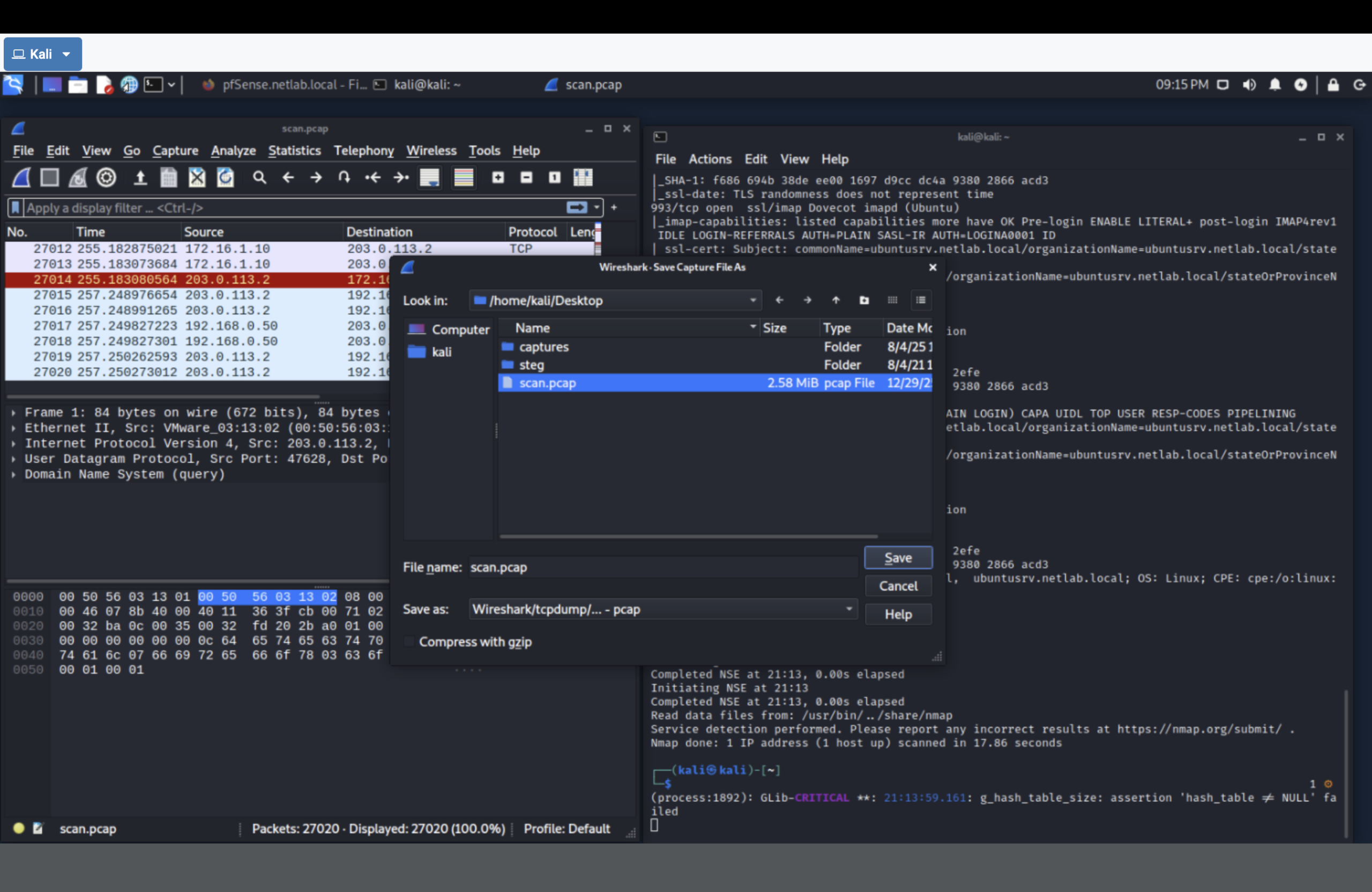
scan.pcap (ground-truth evidence for ingestion).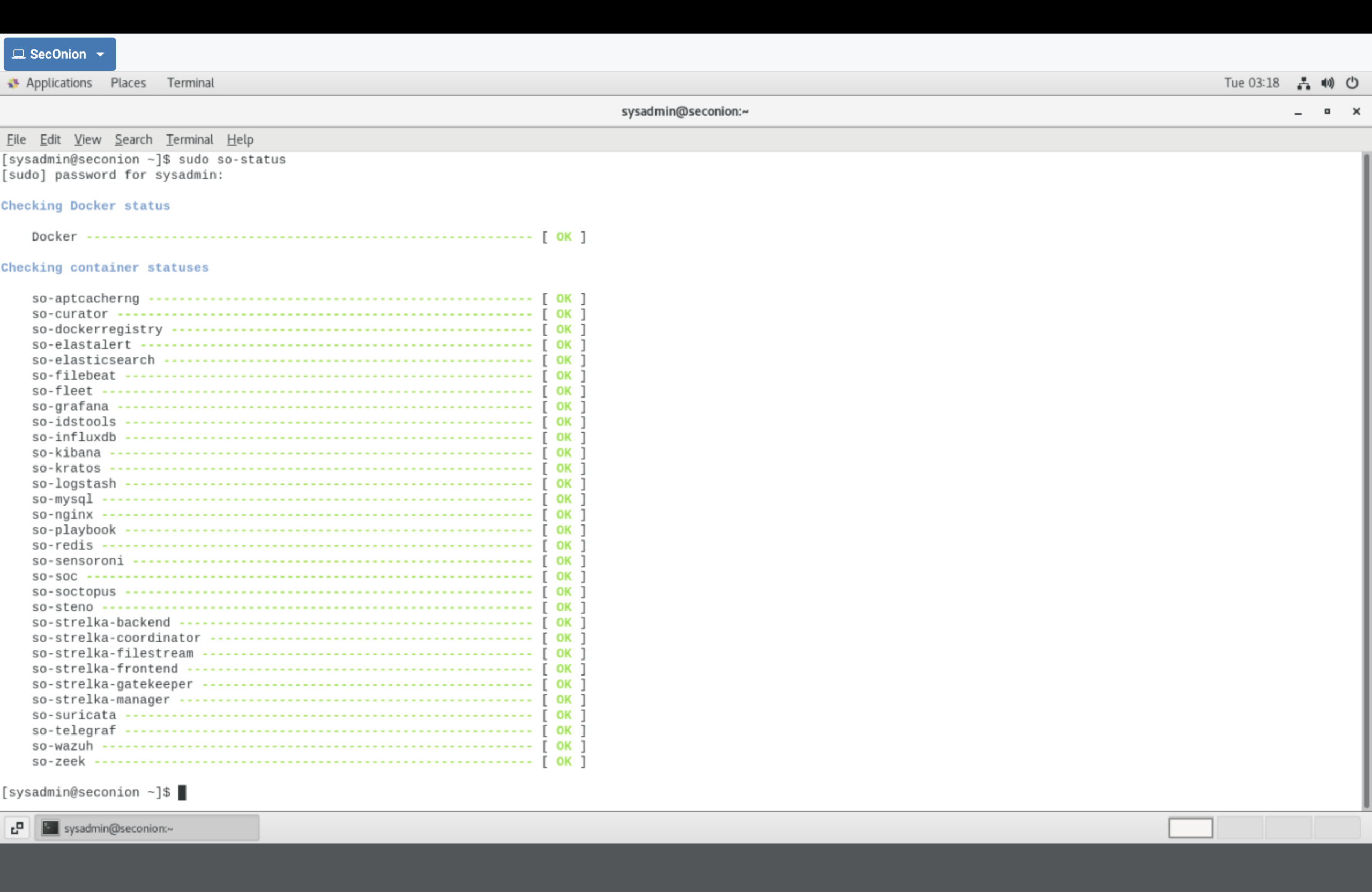
so-status) before importing evidence.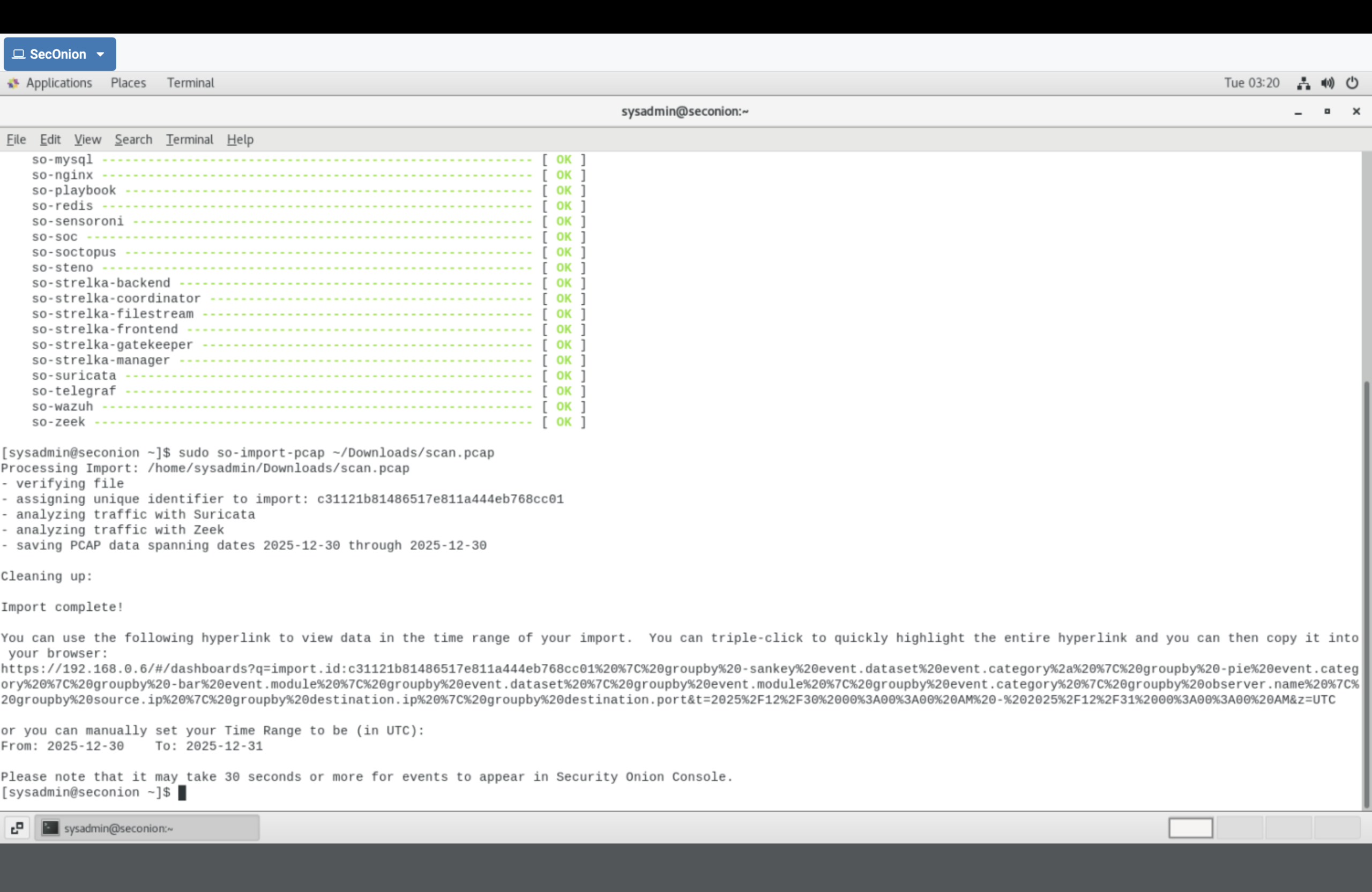
so-import-pcap) to generate detections from the captured traffic.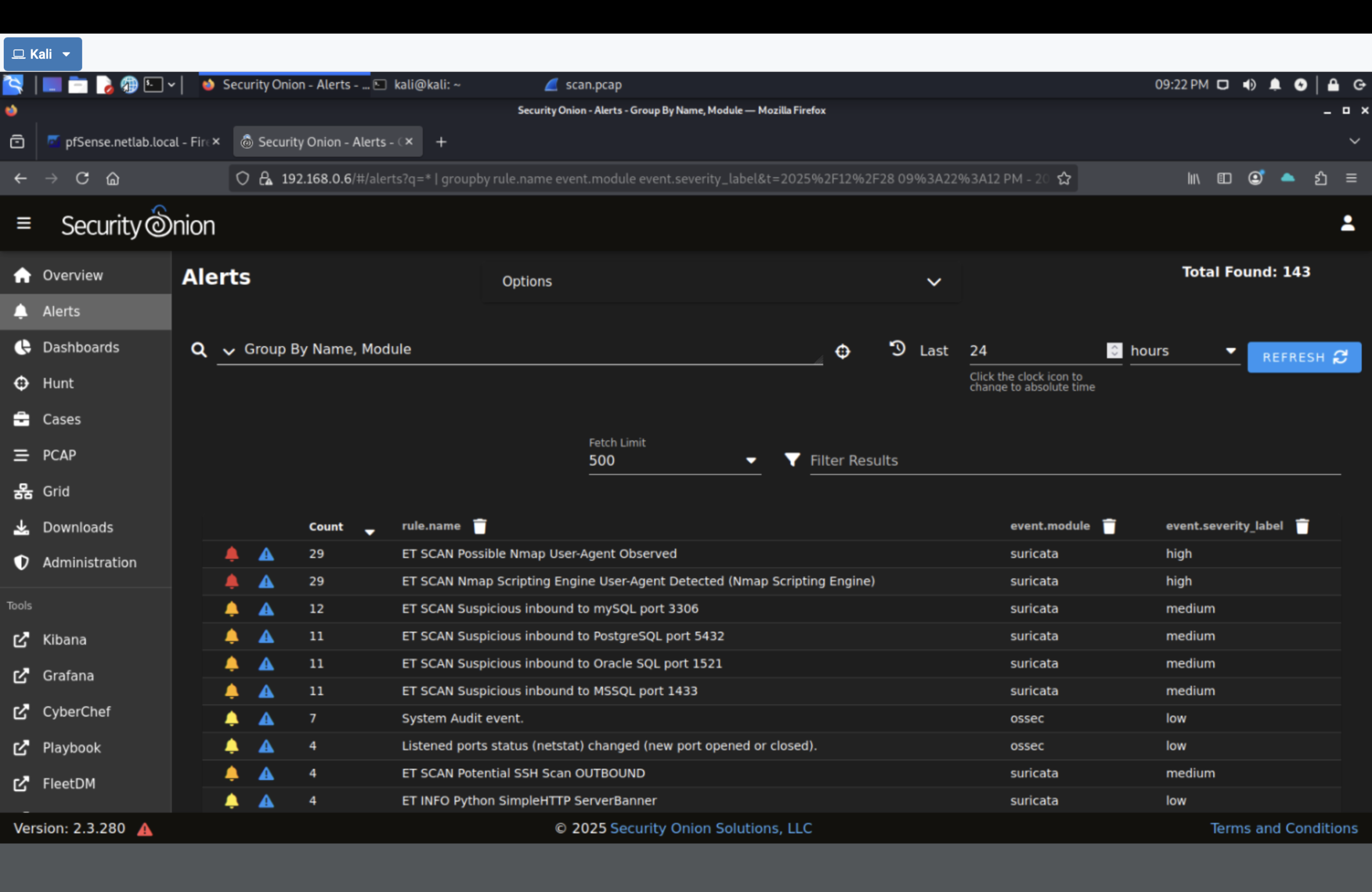
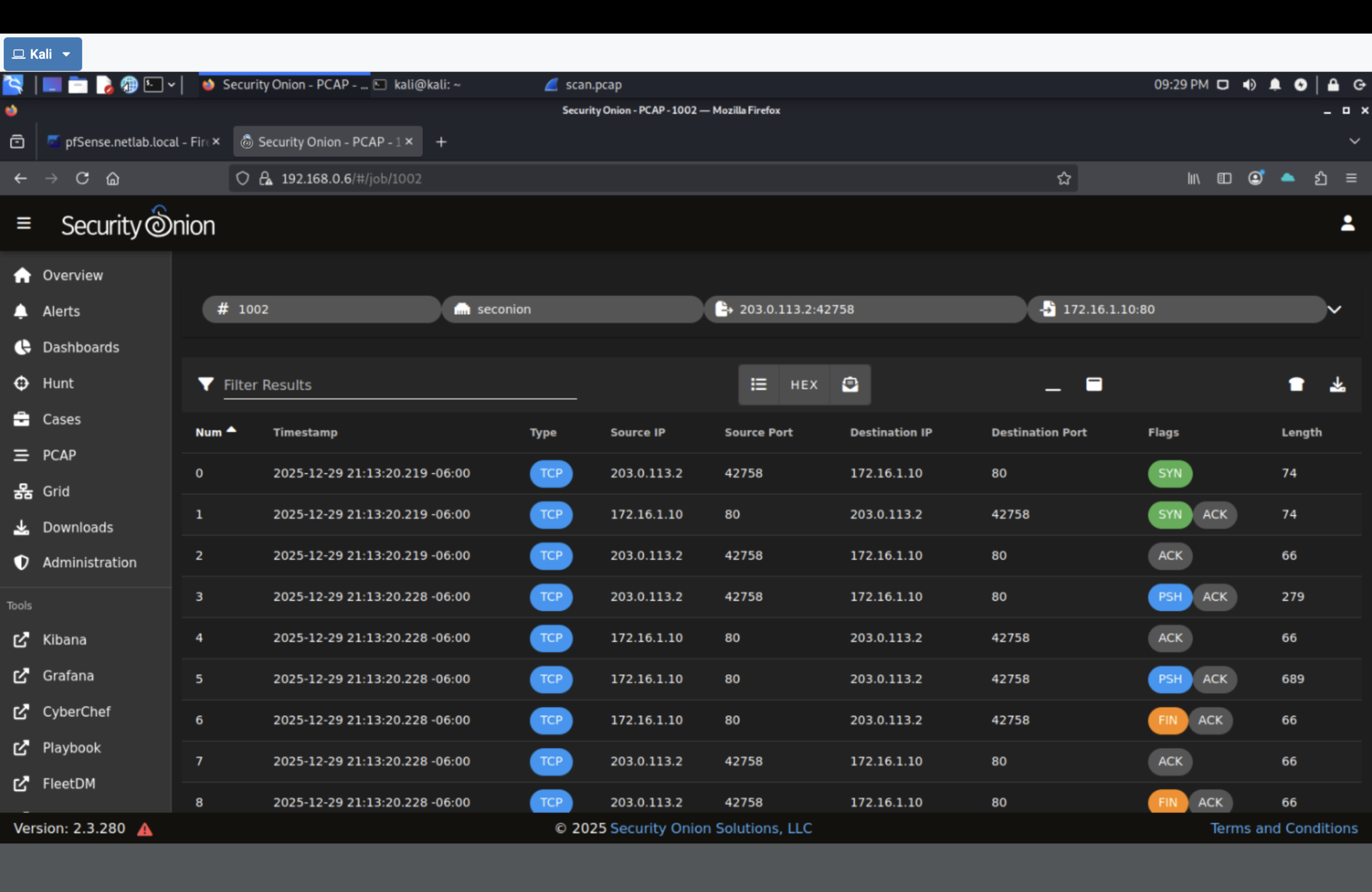
203.0.113.2) and evidence tied to the rule.
Result
- Captured and preserved recon traffic as PCAP evidence.
- Ingested telemetry into Security Onion and validated detections.
- Investigated an alert via drilldown and packet evidence.
- Demonstrated the Zero Trust principle: continuous verification after access.
Why This Makes Me Valuable
Firewall rules and VPNs control entry. But real environments fail inside the perimeter.
This lab proves I can turn raw network behavior into detections and an investigation outcome—bridging
engineering controls with security operations evidence.